Wow, this is a very complex exploit, involving bits of iMessage and an undocumented CPU feature that allowed the attacker to evade hardware memory protection. From what I can see, Lockdown mode would have prevented this. The attacker is ridiculously skilled regardless
Exerpts from the article missing from the bot summary:
The mass backdooring campaign, which according to Russian officials also infected the iPhones of thousands of people working inside diplomatic missions and embassies in Russia, according to Russian government officials, came to light in June. Over a span of at least four years, Kaspersky said, the infections were delivered in iMessage texts that installed malware through a complex exploit chain without requiring the receiver to take any action.
With that, the devices were infected with full-featured spyware that, among other things, transmitted microphone recordings, photos, geolocation, and other sensitive data to attacker-controlled servers. Although infections didn’t survive a reboot, the unknown attackers kept their campaign alive simply by sending devices a new malicious iMessage text shortly after devices were restarted.
The most intriguing new detail is the targeting of the […] hardware feature […]. A zero-day in the feature allowed the attackers to bypass advanced hardware-based memory protections designed to safeguard device system integrity even after an attacker gained the ability to tamper with memory of the underlying kernel.
someone was made fun of one too many times about having green bubbles in imessage
The true villain origin story
i’m a bit of a texter myself, you know…
And it was all Apple’s fault for creating the problem and Batman never stopped them
Seems like the definition of advanced persistent threat.
It isn’t persistent over a reboot, but the tested devices received new corrupted iMessages immediately after reboot
Persistent in APT isn’t referring to the malware itself, but rather the threat actor. I meant that this seems like a textbook APT actor.
You know what else was also super sophisticated, chained, and confident enough in it’s APT to not be persistent across reboots? DOUBLEPULSAR.
Removed by mod
Reminded me restart all my devices
With that many exploits being used I wouldn’t be surprised to see it is a group probably government sponsored. They love iMessage exploits as original attack vectors too.
Russian authorities say it was the Americans trying to spy on other NATO nations, Israel, and Ukraine. America spying on Russia’s enemies.
Well, I may be under the wrong impression but it occurred to me that the US govt likes to spy on everyone, friends and foes and the US citizens, too
Edit: punctuation
Documentary about the pheonix software explains a lot about who used this kind of virus, mainly political figures and govermants to spy on other politicans and jornalists. The imessage exploit was known for a few years but nobody knew how the file installed itself on the device, so there was no way to figure out how to protect the device.
Which documentary?
It’s not purely talent that allows them to make this kind of stuff. Otherwise people outside of these agencies would be making this stuff too. It’s also the fact the CIA or any of the others can go to apple for example and get all of the information on how these chips are made and the firmware on them, then put the company under a gag order.
It is silly to assume the governments hackers are any better then a good hacker that doesn’t work for them. And you need to realise that their advantages come from legal power, resources, and lesser regulations on research.
Because a lot of silly conspiracy theories seem to stem from people believing that the government are somehow superior beings, when the only thing that makes them different from anyone else is power.
Yup. The government has historically had issues keeping good hackers on their payroll. Because the good ones can make way more money in the private sector, so what incentive do they have to actually stick around?
There’s also the issue that the federal government has been required to drug test due to regulations requiring all federal employees to be tested. And good luck finding a good hacker who would be willing to take a drug test.
The only real edge the government hackers have is that they can force companies to give them insider access.
If you hire the hackers that tried to hack you instead of sending them to prison, you can fix the talent retention problem, but I think they already figured that out. Wonder if the kid who hacked GTA is being looked at in that way or if they don’t want to deal with his mannerisms.
This happens rarely, and if it happens, the chances of it being someone we know from the media are almost 0; that would be all under the table. The “best” are the ones you don’t hear about because they are too busy working on actual stuff, same in most science fields.
Most of them are recruited in “normal” ways; there is much more talent around these days. No need to engage with criminals and put them on actual sensitive stuff. Also, they get paid more than you might think; the people leading these projects are not stupid and make a simple mistake like underpaying talent they still need.
They consider him insane. They aren’t letting him close to anything important.
wasn’t that a social hack mainly? what need would they have for social engineering.
Dude hacked again from within his hotel using the tv right? I wonder who’s in charge of doing that math. Hacker skill vs idiosyncrasies
The exploit’s sophistication and the feature’s obscurity suggest the attackers had advanced technical capabilities
exploiting a vulnerability in an undocumented hardware feature that few if anyone outside of Apple and chip suppliers such as ARM Holdings knew of.
according to Russian officials also infected the iPhones of thousands of people working inside diplomatic missions and embassies in Russia
the devices were infected with full-featured spyware that, among other things, transmitted microphone recordings, photos, geolocation, and other sensitive data to attacker-controlled servers
Sounds like government espionage
puts tinfoil hat on
4 zero days means they bought it on black market at least.
I recently invented a “People First” Cybersecurity Vulnerability Scoring method and I called it CITE, Civilian Internet Threat Evaluation with many benefits over CVSS. In it, I prioritize “exploit chains” as the primary threat going forward. Low and behold, this new exploit, although iOS, possibly one of the most sophisticated attacks ever using one of the longest exploit chains ever! Proof positive!
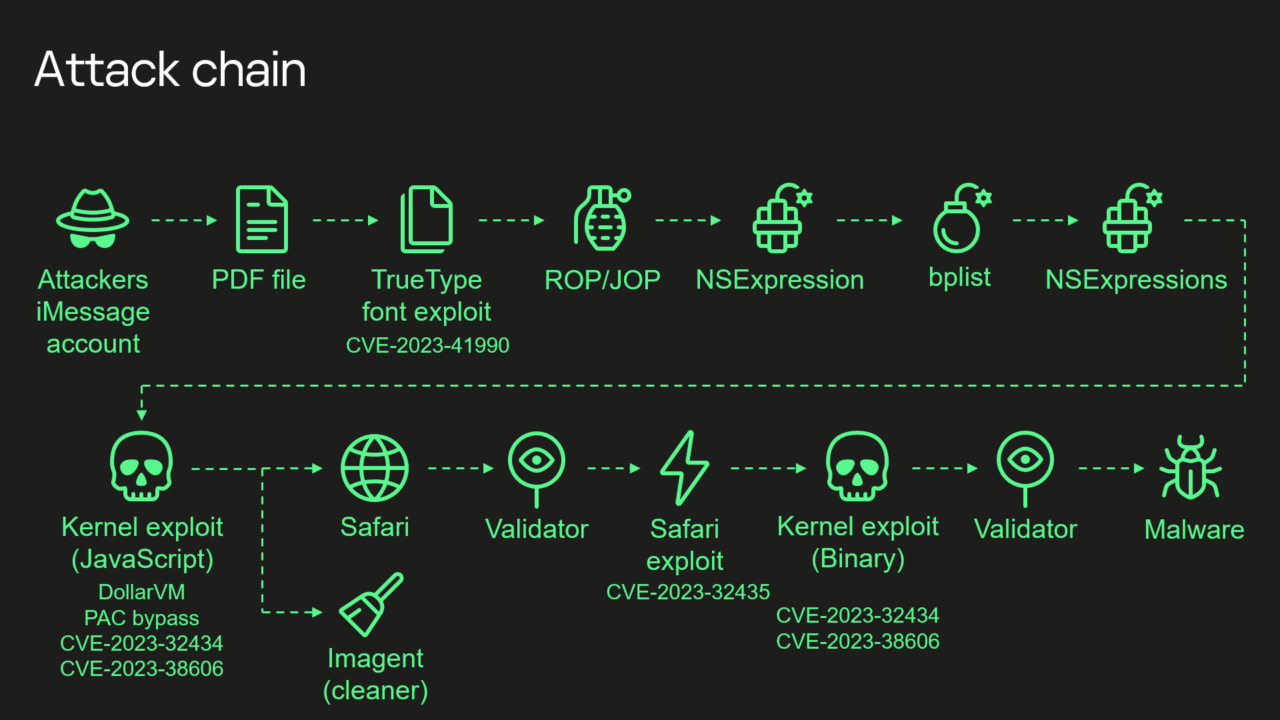
Depending on how you define it; I define the Kaspersky diagram has 8 steps. In my system, I define steps that advance the exploit discretely as stages, so I would evaluated Triangulation to be a 4 stage exploit chain. I should tally this attack to see how it scores and make a CITE-REP(ort).
You can read about it if interested. An intersting modeling problem for me was does stages always equate to complexity? Number of exploits in the chain make it easier or harder to intrusion detect given that it was designed as a chain, maybe to prevent just that? How are stages, complexity, chains and remediation evaluted inversely?
Removed by mod
That’s Standards, isn’t it?
Edit: yup
is this how people who quote Bible verses feel? i can just surmise the meaning by the number and the context because I’m so familiar with the source
I just surmise by the context and end up usually correct so the numbers haven’t quite clicked in yet
It must be, cause I immediately recognized the numbers.
no garfield 3:16
Glancing through your article, while you have correctly assessed the need for risk based prioritization of vulnerability remediation and mitigation, your central premise is flawed.
Vulnerability is not threat— CVSS is a scoring system for individual vulnerabilities, not exploit chains. For that, you’ll want to compare with ATT&CK or the legacy cyber kill chain.
Help me understand your glancing criticisms that I’m taking with a grain of salt.
- You didn’t mention the central premise that is flawed, what do you think it is?
- I’m not confused about vulnerability and threat, what specifically did read to you give you that impression?
You mention that CVSS, which I hold Certification in, is for scoring single threats which I said so many times that is why I made such a system, to depart from CVSS singular, that is inadequate in being singular and common. Glance again?
Compare what with attack? Also, if you mean Lockheed Martin Cyber Kill Chain, that has nothing to do with scoring, that is the methology OF the attack and defense of it, not the attack itself, is a defensive strategy includng reconaissance and nothing to do with scoring.
- From the title of your article and your executive summary, the premise of your paper is that CVSS is flawed, and CITE is your solution.
- From the title of your article, and choice of name, “QHE CVSS Alternative; CITE”. CVSS is a VULNERABILITY Scoring System. CITE, as your propose, is a THREAT evaluation tool. You can see how one could have the impression that they were incorrectly being used interchangeably.
As you yourself stated, CVSS does exactly what it says on the box. It provides a singular rating for a software vulnerability, in a vacuum. It does not prescribe to do anything more, and it does a good job doing what it sets out to do (including specifically as an input to other quantitative risk calculations).
Compare what with attack?
Your methodology heavily relies on “the analysis of cybersecurity experts”, and in particular, frequently references “exploit chains”, mappings which are not clearly defined, and appears to rely on the knowledge of the individual practitioner, rather than existing open frameworks. MITRE ATT&CK and CAPEC already provide such a mapping, as well as a list of threat actor groups leveraging tactics, techniques, and procedures (e.g., exploitation of a given CVE). Here’s a good articlewhich maps similarly to how we operate our cybersecurity program.
I think there is a lot on the mark in your article about the issues with cybersecurity today, but again, I believe that your premise that CVSS needs replacing is flawed, and I don’t think you provided a compelling case to demonstrate how/why it is flawed. If anything, I think you would agree that if organizations are exclusively using CVSS scores to prioritize remediation, they’re doing it wrong, and fighting an impossible battle. But this means the organization’s approach is wrong, not CVSS itself.
Your article stands better alone as a proposal for a methodology for quantifying risk and threat to an organization (or society?), rather than as a takedown of CVSS.
Ah, much better. MITRE CWSS + CWARF is comprehensive, yet insular and as is MITRE, Military/NATSEC Focused. I do not see any flaws in my reasoning, but words as communication. I do concede that maybe my saying an alternative to CVSS is not really the best wording as I see such things in very broad terms, but I get the perspective now. As in, the common singular, Gov/Corp system does not fit, I need an alternative model that does. In contrast to I need another exactly scoped system that does it differently alternative.
To evidence this I can point to that fact that I even advocated that CVSS-BTE v4.0 should be NVD baseline, but I didn’t make this very clear that I’m expanding the CVSS as an alternative use, different in applicability, essential in nature, and somewhat built upon CVSS and OWASP with a different, very important objective.
Not replacment which I never intended… I’ll change the article to reflect those views, well done.
Thanks for sharing! I’m amazed at how sophisticated this was.
This is the best summary I could come up with:
Researchers on Wednesday presented intriguing new findings surrounding an attack that over four years backdoored dozens if not thousands of iPhones, many of which belonged to employees of Moscow-based security firm Kaspersky.
Chief among the discoveries: the unknown attackers were able to achieve an unprecedented level of access by exploiting a vulnerability in an undocumented hardware feature that few if anyone outside of Apple and chip suppliers such as ARM Holdings knew of.
“The exploit’s sophistication and the feature’s obscurity suggest the attackers had advanced technical capabilities,” Kaspersky researcher Boris Larin wrote in an email.
“Our analysis hasn’t revealed how they became aware of this feature, but we’re exploring all possibilities, including accidental disclosure in past firmware or source code releases.
A fresh infusion of details disclosed Wednesday said that “Triangulation”—the name Kaspersky gave to both the malware and the campaign that installed it—exploited four critical zero-day vulnerabilities, meaning serious programming flaws that were known to the attackers before they were known to Apple.
The researchers found that several of MMIO addresses the attackers used to bypass the memory protections weren’t identified in any device tree documentation, which acts as a reference for engineers creating hardware or software for iPhones.
The original article contains 653 words, the summary contains 200 words. Saved 69%. I’m a bot and I’m open source!
There are few groups I think they could pull off such a stunt and would even want to. Nation state actors from the US such as CIA/NSA, or China, like the Ministry of Industry and Information Technology. They have a many other gov sectors with very talented APT groups. I’d bring up that NK nation state actors are also very talented, but they’ve been recently aligned with Russia. Perhaps their loyalty to the CCP is stronger than their current Russian ties.
Skill is certainly one evaluation parameter and Fin7, JokerStash, Carbanak fit that bill but that is not their MO. Target, motive, opportunity -> Embassy Employees/Diplomats -> Nation-State or Intergovernmental Group (like 5/9/14 eyes) as eval combined with skill rating, @95% confidence.
deleted by creator
I wonder how many of those exploits were long known by the three-letter agencies, and were hoarded instead of getting fixed.
Can’t wait to listen to the Darknet Diaries interview about this in a few years.
How do you find those podcasts, sometimes the stories are really interesting but I think he is running thin on ideas.
not op, but I think it depends a lot on the person he’s interviewing
It’s important to reboot your devices frequently
Does ios have any ROP mitigations?
deleted by creator
Can the US government pass a law to force Apple specifically to rip out the messages app and replace it with something that apparently doesn’t have infinite exploits??
There is no such thing as a device or software without exploit, even a carrier pigeon can be cought and the messege read.
What if the pigeon has a gun?
That’s it boys. We’ve found the answer. Pack it up
iGun patch incoming
You are thinking of exploding penguins.
Not if you wirte the message using invisible ink.
Not if you never write the message, more like
I wouldn’t trust a service whose source code is not accessible though.
We may not have carrier pigeon DNA readily available, but it is certainly accessible!
How would that help them? Even if that were an effective measure (which it isn’t), it was almost certainly a us spy agenciy that did this.
Not necessarily, five eyes share intelligence responsibilities