- cross-posted to:
- [email protected]
- cross-posted to:
- [email protected]
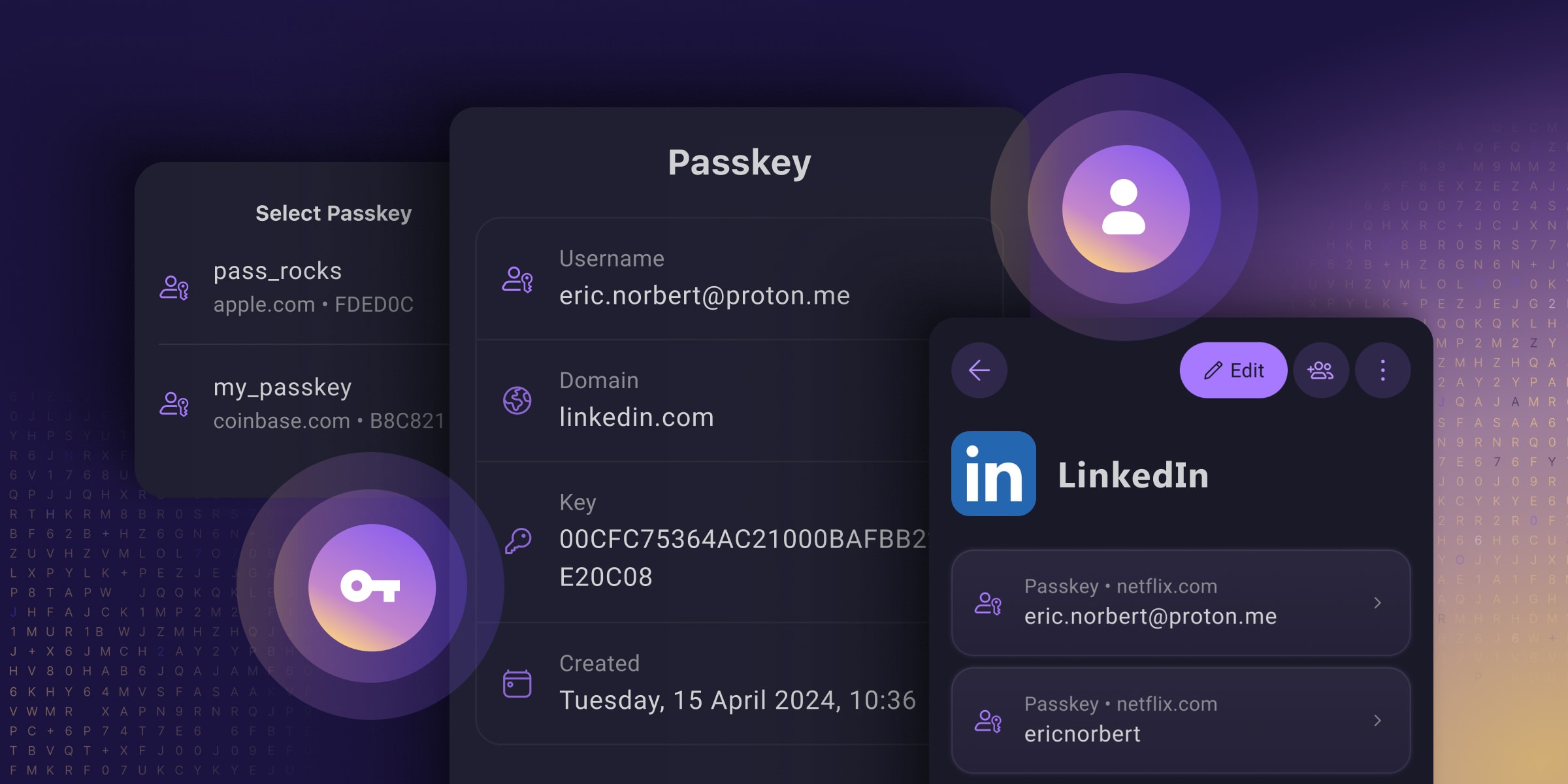
Passkeys are an easy and secure alternative to traditional passwords that can help prevent phishing attacks and make your online experience smoother and safer.
Unfortunately, Big Tech’s rollout of this technology prioritized using passkeys to lock people into their walled gardens over providing universal security for everyone (you have to use their platform, which often does not work across all platforms). And many password managers only support passkeys on specific platforms or provide them with paid plans, meaning you only get to reap passkeys’ security benefits if you can afford them.
They’ve reimagined passkeys, helping them reach their full potential as free, universal, and open-source tech. They have made online privacy and security accessible to everyone, regardless of what device you use or your ability to pay.
I’m still a paying customer of Bitwarden as Proton Pass was up to now still not doing everything, but this may make me re-evaluate using Proton Pass as I’m also a paying customer of Proton Pass. It certainly looks like Proton Pass is advancing at quite a pace, and Proton has already built up a good reputation for private e-mail and an excellent VPN client.
Proton is also the ONLY passkey provider that I’ve seen allowing you to store, share, and export passkeys just like you can with passwords!
See https://proton.me/blog/proton-pass-passkeys
#technology #passkeys #security #ProtonPass #opensource

Removed by mod
I’m not saying it doesn’t count as authentication, it just doesn’t count as authentication to the security of the server directly. That’s the device’s security and configured by the user, not the server. And user devices are very prone to exploits to the point that many law enforcement agencies don’t even bother asking for a password anymore to access a device.
So, let’s move to a physical model as an example. Let’s say you have a door. It has a very simple door handle lock. You keep your key inside a hotel safe. Sure it might be difficult to get the key if they had to enter the hotel room, cut open the safe in place, and get the key while they’re standing in front of the secure door, exposed. But that’s dumb. They could just as easily grab the safe out of the room and open it later where there’s room for proper equipment, use a known exploit for the particular safe, or use other exploits all out of view of the door/server and at any time until the user realizes you know how to open their safe, because the door/server will never find out. Once that safe is open, you have not just the key to the door, but the key to all locks the user uses since now we only have “something you have” factors and the user uses only one device. Just like when we only had “something you know” factors and the user uses the same password everywhere.
So what does the passkey help with? It makes the lock and thus the key itself more complex. This makes it so that brute force attacks against the server are more difficult. But it doesn’t solve anything that existing TOTP over text messages didn’t solve, other than some complexity, and it eliminated the password (something you know) factor at the server. Something a lot of companies are already doing and we already know from experience is a bad practice. It has changed the hacking target to the device rather than the person. But still just one target, you don’t need both. Sure it’s better than a really bad password that’s reused everywhere. But it’s not better than a really good password unique to a site that’s only stored in a password manager on the user’s device that requires a separate master password to access (outside of MitM attacks that TOTP mitigates).
Now, what if we have a door with two locks, one that requires a code, and one that requires you to have access to a device. Now in order to attack the door, you need two factors right at the time you’re standing at the door. Also, there’s probably a camera at the door and someone paid to check it periodically when someone tries too many times, which isn’t the case in the user’s safe/device. So even if you get the key from the user, you still need to brute force the second lock efficiently or you need to implement a second exploit to get the second factor ahead of time. This is the idea of two factors at the server and the current state of things before passkeys.
Removed by mod