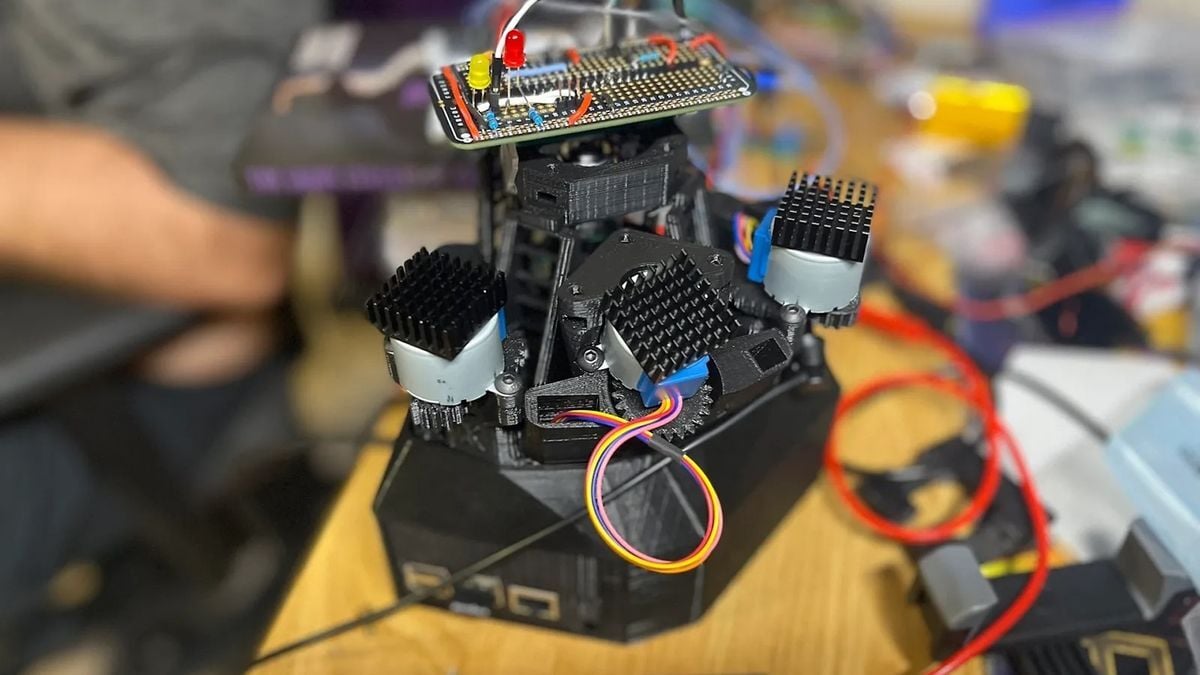
… "The first of two versions of the RayV Lite will focus on laser fault injection (LFI). This technique uses a brief blast of light to interfere with the charges of a processor’s transistors, which could flip them from a 0 value to a 1 value or vice versa. Using LFI, Beaumont and Trowell have been able to pull off things like bypassing the security check in an automotive chip’s firmware or bypassing the PIN verification for a cryptocurrency hardware wallet.
The second version of the tool will be able to perform laser logic state imaging. This allows snooping on what’s happening inside a chip as it operates, potentially pulling out hints about the data and code it’s handling. Since this data could include sensitive secrets, LSI is another dangerous form of hacking that Beaumont and Trowell hope to raise awareness of." …
Hack the planet!

starts attacking the ground with an axe
Hack the planet!
They’re trashing our rights! Trashing!
Security chips like smart card processors have safeguards against this sort of attack, fwiw. Regular chips are likely more vulnerable.
Safeguards against LSi may include :
Sensor-based detection ?
Error detection and correction ?
Redundancy and duplication ?
Shielding // physical + chemical protection ?
Anti-tamper mechanisms ?
Randomization and noise injection ?Chapter from “Security Engineering” (2nd ed) about physical tamper resistance:
https://www.cl.cam.ac.uk/~rja14/Papers/SEv2-c16.pdf
It’s been ages since I read it so idr how much of it was at chip level. Really high end stuff have the secure chips in a tamper reactive enclosure so it’s difficult to get to them without first erasing the contents. The chapter discusses that ;).
Why the question marks, the answer is always yes.
Because this is not my domain of expertise and I seek comments from other people.
I was gonna ask if things like YubiKeys or even security chips inside smartphones were vulnerable to these sort of attacks, but apparently not, thanks for the heads up.
I don’t think perfect invulnerability is possible: there are just higher and lower amounts of resistance, and of course there can be mistakes including in the protocols. The really high end stuff with tamper reactive packaging (e.g. used in banking) are usually installed in servers in secure data centers, with 24/7 CCTV coverage. So it would be very hard to mess with those things without at least being detected on the camera. The chips inside phones (Apple Secure Enclave, Google Titan) do receive a lot of attention to these issues.
Back around the 1990s there was sort of a technical arms race between set-top box manufactuers (the boxes authenticate to the networks with smart cards) vs cable TV pirates (they were willing to spend lots of money breaking cards, so they could sell illicit pirate cards to people). I think in the end, the card manufacturers “won” (made cards that the pirates couldn’t beat), but I don’t know if they have kept that advantage for all these years since then.
i have doubts since, from the article, they were able to be : “bypassing the PIN verification for a cryptocurrency hardware wallet” … so i am waiting and looking for more sources and confirmations.
Edit → in header
… "The first of two versions of the RayV Lite will focus on laser fault injection (LFI). This technique uses a brief blast of light to interfere with the charges of a processor’s transistors, which could flip them from a 0 value to a 1 value or vice versa. Using LFI, Beaumont and Trowell have been able to pull off things like bypassing the security check in an automotive chip’s firmware or bypassing the PIN verification for a cryptocurrency hardware wallet.
The second version of the tool will be able to perform laser logic state imaging. This allows snooping on what’s happening inside a chip as it operates, potentially pulling out hints about the data and code it’s handling. Since this data could include sensitive secrets, LSI is another dangerous form of hacking that Beaumont and Trowell hope to raise awareness of." …
Edit #2 : Can’t find this laser fault injection (LFI) on WikipediaWaiting for some MFer to use that shit to cheat it SM64 speedruns… or maybe a TASbot module. 🤔