All I know is that if you’re very worried about being surveilled by governments, the Fediverse is the absolute last place you should want to be.
This is one of the most transparent platforms we have come up with yet. Instead of all your data only being viewable by a host company, it’s viewable and able to be analyzed by basically anyone who puts some effort in. This makes it economically worthless, can’t really sell something that everyone can already just get for themselves.
We’re all out in the open here. So, wave to all the national security agencies everyone. Hiiiii! Hope you’re all enjoying the memes!
deleted by creator
Most of the big social networks are owned by US companies. Those are forced to disclose user data to the US intelligence agencies, by the PATRIOT act and CLOUD act. And those will share it with the 14 Eyes.
So, you are right about Lemmy, but it’s not true that data on traditional social media is only viewable by the host company.
Let’s not forget that classic corporate social media companies generally have way more information on their users as well.
I’ve gotta get busy posting dick pics then
What data does Lemmy log?
Very little in its current form, I think mainly just IP address.
Nah, most governments can just buy that data from the most of the VPNs if they need to - no need for secrecy.
If you think nord VPN is protecting you from government surveillance I have a bridge to sell you - it’s really affordable.
How about Mullvad?
(https://www.theverge.com/2023/4/21/23692580/mullvad-vpn-raid-sweden-police)Now that they’ve finished going RAM only it’s even more secure
And for $5 a month you’re losing money not using them.
deleted by creator
Fuck that sounds exciting. Could I timeshare that shit?
“from the most of the VPNs”
Aah, which VPN is “the most”?
That’s a good question. If you don’t know and trust the VPN owner you should be careful… that’s why a lot of folks who specifically use a VPN for security reasons and have very good reasons to need to do that often just self-host a private VPN/tunnel exit.
Also considering you don’t know me (still waiting on that coffee you said we’d grab) you probably shouldn’t trust any list I gave you anyways.
That all said - Nord is probably on that list.
I fear false privacy because a corporation runs it. I’ve never been afraid of a government but I worry about corporate shittery all the time.
deleted by creator
deleted by creator
deleted by creator
Still the government you should be afraid of as well in this case, though.
I use a VPN to stop work camps I stay at from knowing what porn I watch, to stop media companies from sending me copyright infringement notifications, and to stop public wifis from having as much info on me.
Its all about threat model. If you’re concerned with government actors then you need to be more secure than just a VPN.
My countries intelligence agency is not working with media companies like that. The cops and courts would eventually enforce some order against me if it ever went to court but more likely is my ISP just ditches me as a customer if I get too many strikes.
deleted by creator
Well there are only three isps here and yes I understand what you are saying but. It never gets as far as government force it doesn’t have too. The ISP will drop me.
Also the ISP is the media company lots of the time, and its only a crime that will go to court and win if I made money distributing copyrighted material.
I don’t want my ISP to know much about what I’m doing either. They aren’t trustworthy, they often get caught illegally shaping traffic and such too.
deleted by creator
Don’t condescend to me. I understand the link between government and capital and am not an american.
What are you even proposing anyways? I am against government oppression and copyright law in general. All private property is theft from the commons. But in the meantime I will use a VPN because I trust Mullvad in Sweden more than I trust my own ISPs.
If I was committing crimes that were more serious then I would not use a VPN I would use a more robust security model.
My ISP is not powerless without government. They have massive power, they control 1/3rd of all cellular and internet communications. And like I said also control large amounts of satellite TV and cable broadcasting.
deleted by creator
History entered the chat
Slightly off-topic rant:
I hate how the ‘VPN’ term has been took over by companies selling services using VPN technology.
VPN was initially ‘Virtual Private Network’ – used to securely connect own (as belonging to an organization or person) devices over a public network. Like securely connecting bank branches. Or allowing employee connect to a company network. And VPN are still used that way. They are secure and provide the privacy needed.
Now when people say ‘VPN’ they often mean a service where they use VPN software (initially designed for the use case mentioned above) to connect to the public interned via some third-party. This is not a ‘private network’ any more. It just changes who you need to trust with you network activity. And changes how others may see you (breaking other trust).
When you cannot trust your ISP and your local authorities those ‘VPNs’ can be useful. But I have more trust to my ISP I have a contract with and my country legal system than in some exotic company in some tax haven or other country that our consumer protections or GDPR obligations won’t reach.
Back to the topic:
I do not believe that all VPN services are owned/funded by governments, but some may be. I don’t have much reason to trust them, they are doing it for money and not necessarily only the money their customers pay them. In fact I trust my government more that some random very foreign company.I cringe when I see people touting VPN services as somehow better than HTTPS.
Sure VPN helps you re-source your IP address but that doesn’t do anything to help the security of online banking.
You know MITM an https website is child’s play, right? If you’re inputting your password on a network you don’t trust you’re doomed. SSL certificates are worthless because they can be easily forged by anyone pretending to be the site as long as they’re between you and the actual site, which they need to be to MITM.
VPN and HTTPS solve different issues, and are better when used together. Most of the time you don’t need a VPN because you trust your home network and ISP, but if you’re using a public access point https does not replace a VPN.
Tell me more about SSL certificate forgery. As far as I know, for a device to trust it, it needs to be signed by a trusted CA. You’d either need to compromise a CA and create your own certificate for the website or make the target device trust a custom CA. In the case of a custom CA, the user explicitly needs to perform an action to trust it. How is this not enough on a public network?
There are cases of malicious/incompetent CAs issuing certificates to parties who don’t own the domains. DigiNotar was the most famous one, and recently there was a Chinese CA (I forgot the name) booted from the list as well. Once they’re detected (browsers report SSL certs they see back to mothership for audit) they would be removed from trusted lists though, so chance that they’re only used for high value targets and can’t be used that often.
There are several ways, most common is to MITM the address to redirect to a different but similar one, which is unlikely to get noticed since you know you typed the address correctly or you clicked from a trusted link/favourite, then that wrong address has it’s own valid SSL certificate. Another way is to use self-signed certificates, which browsers would warn people about, but apps are not likely to. Also you can MITM the CA themselves, whole you wouldn’t be able to actually pass by them you can do an exhaustion attack and essentially block all certificate exchanges, yes your site won’t have a valid certificate, but neither will any real site, so most people will just ignore the message the browser is showing them because it’s showing it for every site.
None of these methods would fool an attentive educated person, but they might fool someone in a rush. Also even if the attack doesn’t succeed in stealing information it 100% succeeds in blocking access, while I might not be as concerned about blocking my Facebook, blocking my bank might prevent me from doing important stuff, and worse people who need to get into their bank are likely to just wave security warnings out of the way without reading them, especially if they’ve been getting them for everything else and nothing had a problem.
Edit: I also forgot to mention the other ways, there are leaks from CAs constantly, which allow you to either impersonate them or sign other certificates. Sure these get patched rather quickly once found, but after you have the signed certificate from them it’s game over. Also what I was referring in the other post is self-signed certificates, most browsers show a warning about them nowadays, but again you can win by exhaustion.
You went from “MITM TLS is child’s play” to “there are some ways we can social engineer our way around it if the stars align just right” in like one post. You’re clearly not qualified here, stop with the FUD bullshit.
Yes, I trust my ISP more than my VPN, but I trust my VPN more than I trust the random wi-fi in the shopping mall. Using a VPN in your house for internet access is pointless, unless you’re purposefully trying to keep your ISP out of the loop for legal reasons, e.g. Torrent, but MITM a VPN is much harder to do than an open wi-fi.
I hate how the ‘VPN’ term has been took over by companies selling services using VPN technology.
Agreed. What they’re really selling is a proxy service, I don’t know why that term isn’t used. The fact that VPN software is used to establish that proxy isn’t relevant, the end result is a proxy.
How is the term “proxy” more appropriate though? It’s also the technical name for a concept that already exists. VPNs are by definition broader in scope than proxies, they work at a lower level of the networking stack and have different capabilities even if most people don’t take full advantage of it. Anyway the point is that it’s not a more appropriate term.
AFAIK the only thing VPN providers let you do, like SurfShark, ExpressVPN, NordVPN, ProtonVPN etc., is to route all of your outgoing traffic through their servers. They don’t allow you e.g. to be in the the same fake LAN as a friend, which is what a VPN does.
Quote from Wikipedia:
A proxy server that passes unmodified requests and responses is usually called a gateway or sometimes a tunneling proxy.
That’s pretty much what those commercial “VPN” providers offer.
They don’t allow you e.g. to be in the the same fake LAN as a friend, which is what a VPN does.
That’s not what a VPN does, that’s what a VPN can do, if desired. What a VPN does is set up an encrypted tunnel between you and some remote network. That’s it. How that remote network is laid out, how the traffic (and also what kind of traffic) is routed into/through/out of that network, and what the clients are allowed to do within are entirely up to the wishes of the network’s owner. It might very well choose to isolate you from all the other clients on the network; that’s not just a possibility, it’s actually one of VPN’s most important, most useful features.
That’s pretty much what those commercial “VPN” providers offer.
Those commercial VPN providers offer you a fully encrypted tunnel that you can route all your network traffic through if you wish. It’s just that people don’t generally use it as anything more than just a proxy. Still, the connection is a textbook VPN connection, it’s there, and it’s capable of things a regular proxy is not, if you choose to make use of them.
Lucky you to be able to trust your ISP. Mine injects ads whenever they can, even hijack DNS and redirect invalid/blocked domains to a page full of ads.
In correct law, that’d be copyright-violation committed by your ISP:
IF the website you hit didn’t authorize your ISP to create a derivative-work,
THEN your ISP adulterating it should be considered commercial-copyright-violation, and stomped by the copyright-lobby.
Notice how this has been going-on for decades, and the copyright-lobby … ignores it, to stomp-on individuals only…
Interesting evidence of “rule of ‘law’”, isn’t it?
Fun fact, TOR was created by the US navy.
As a way for spies to communicate anonymously and securely.
That’s what they want you to think 😉
Nope, that’s literally what onion routing is about in case you aren’t being facetious. It’s in the whitepaper and in the code. It’s also in the Snowden leaks.
Edit:
Lemmy doesn’t allow direct image posting anymore?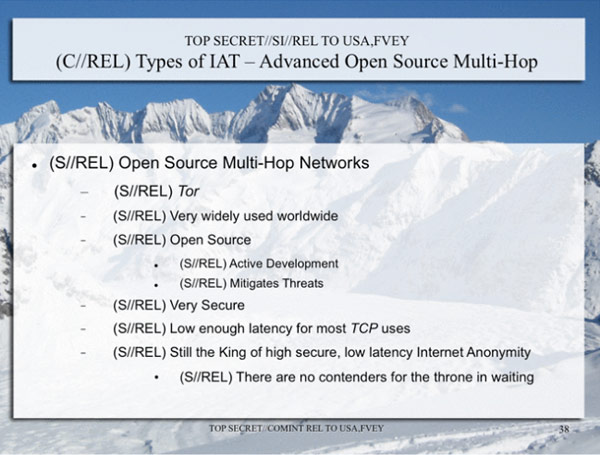
Of course that was a long time ago, and hidden services may be much more easily compromised now. And they’ll always have their precious 0days. Don’t traffick kids, terrorism, or ounces of pure fentanyl and tor will work just fine for you.
and hidden services may be much more easily compromised now
In the end it’s still just a site on a server, if it’s poorly configured or not secured well it’s as vulnerable as any other on the clear net. Once they’re able to work out where it is it becomes a honey pot shortly afterward.
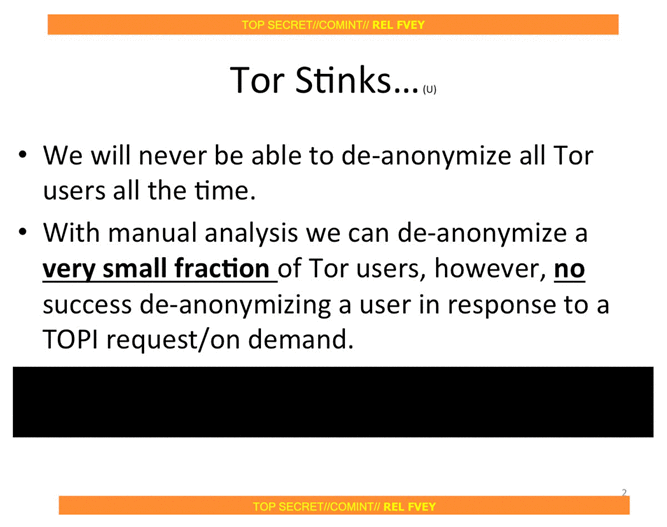
Yes, but with the amount of darknet markets and CSAM hidden services that have been taken down within a relatively short span of time compared to the last decade of tor’s more widespread history, it seems they may have a new vulnerability (or perhaps just a new covert post-snowden-acceptance surveillance court ruling) that allows them to identify hidden services real IP addresses. It’s speculation, but they wouldn’t use it bluntly or everyone would know there was a vulnerability and thousands more eyes would be on the tor code (or awareness of nation-state level traffic omniscience in the case of something as simple as a timing attack). A CSAM hidden service has been run by the federal governments of a few countries, so there’s no question of ethics or law in that case.
The “users” are probably the weak point. Badly configured setups leaking info, aggregation using that info to fingerprint a user, etc. When they have a user account with access they can use it to keep collecting data and digging. I imagine it’s a slow process. Nothing networked can be 100% secure though.
deleted by creator
deleted by creator
deleted by creator
Why is “governments” the boogeyman that comes to mind? Scammers and thieves would have much more interest in your everyday consumer internet usage.
Haha, nice try governments
What exactly do you mean by “scammers and thieves”? The only protection you get from a VPN is privacy from your ISP. That ISP obviously operates in your country (there has to be some physical connection) and is regulated by your government. It’s easy for the government to demand data from the ISP about you (or about certain usage patterns and which users have them) without you knowing, not to mention how easy it is for the ISP itself to monetize your usage data.
A scammer or thief can’t as easily grab hold of that data. If you’re imagining a hacker gaining access to the ISP’s database or network, that’s certainly plausible but it’s just as possible with a VPN provider. I personally don’t think the big commercial VPNs are much more secure than ISPs. Maybe a little.
Its mostly protection when using public WiFi against spoofed website. Actually, not just public WiFi, it’s protection when using any WiFi from routers whose owner never changed the default password or using really weak ones.
Did you even read the OP? A VPN that has real customers but is set up by a scammer can be doing anything on your computer. You install their client. It could be a key logger for all you know.
And not all services use end to end encryption so yes there is still the potential to listen to http traffic and extract data from it, especially as the VPN client.
No, but VPNs are a false illusion of privacy. When you use a VPN, you’re really just shifting your trust from your ISP to the VPN company. And governments can just force both to give them the data they have about you
I agree, and of course it’s a matter of trust. I am trusting what the VPN says when they say…they’re physically incapable of storing logs. NordVPN & I think a couple others both claim their services literally don’t store any logs of any kind.
So the feds could come around & demand info, but they shouldn’t have anything.
It is safe to assume that somebody, somewhere, somehow could be watching you or have the capacity to monitor your web activity. If they gave a shit, if they cared enough to hone in on you. ¯\(°_o)/¯
It’s not that simple though. VPN providers in most cases have been externally audited not to store any logs of user activity, meaning they couldn’t comply with government requests of this nature. Generally, their entire legitimacy as companies depends on trust, meaning they have much stronger incentives to actually keep user data private than an ISP does. Of course I agree that using a VPN is no privacy silver bullet, but it’s not like they have zero privacy benefits either.
That’s why you do your research and use a VPN domiciled in a country that won’t budge to requests coming from your country.
This is exactly right. If you really want to browse privately, use Tor.
I feel that if your government really wanted your secrets, they’d just send goons to your house to beat the fuck out of you.
I have a VPN to protect me from nosey bastard piracy lawyers.
100% this. OP is describing a great plot for an B-tier Hollywood movie, but reality tends to be much less thrilling. Obligatory xkcd.
Yeah and the bonus text is how I think. The CIA, NSA or whoever think you’re too boring to bother with. Even if the VPN was directly owned by the NSA, they don’t really care about whatever fetish porn you’re jerking off to. If you’re some kid still in your edgy socialist phase, they don’t care. Sorry, you’re just a basic bitch to them.
Generally speaking, governments aren’t that good at keeping secrets at scale. Government-run VPNs would require a lot of people doing coordinated work; data center employees, ISPs, people passing themselves off as independent auditors, legal teams, marketing teams, and more. The more people you add, the less likely it is to be kept a secret. And all of this across multiple VPN companies (because there’s no guarantee that the person you want to surveil is using the one you own) and internationally (many VPNs are based in or have major operations in multiple countries).
Now, is it possible that the NSA has an undisclosed financial stake in one or more VPNs and has secretly inserted a backdoor? Sure, anything is possible. But is that more likely than them just buying up Ring doorbell footage or doing large data analysis on social media activity? Or installing rootkits on your smartphone firmware? Or just good old fashioned LoJack?
If they have reason to investigate you, they’re going to probably get everything anyway. No reason to make it easy for them by not using a VPN.
The more people you add, the less likely it is to be kept a secret.
This is also one of the most convincing arguments about most conspiracy theories. Most would require so many people to never talk that the secret would be about as secret as North Korea’s fake grocery stores
Indeed. The biggest reason I’m skeptical of conspiracies, honestly.
That’s not how these things work - Intelligence agencies use cover companies very differently. They simply provide a few people money to create a company. These people set up a VPN company - and run it like it’s legitimate.
Marketing or legal won’t know that their company is actually a listening post, most Datacenter employees won’t know, only very few people(mostly network engineers and IT security, some managers)would know. And of course the Auditors - which is not a hassle for any decent intelligence agency.
It’s far easier than one would think - how do we know that? Because it would be the same way other intelligence service companies are run like that for decades.
Oh what a novel idea
Now, is it possible that the NSA has an undisclosed financial stake in one or more VPNs and has secretly inserted a backdoor? Sure, anything is possible. But is that more likely than […]
Yes i guess most of them could be but i don’t think proton is because they are open source and comes under swiss law just to be safe use tor.
Wasn’t Proton forced to log and handover an activist’s data, after a Swiss court order? I feel I read something to that effect a year or two back.
Source ?
- https://arstechnica.com/information-technology/2021/09/privacy-focused-protonmail-provided-a-users-ip-address-to-authorities/
- https://www.privacyaffairs.com/protonmail-surrenders-user-logs/
- https://techcrunch.com/2021/09/06/protonmail-logged-ip-address-of-french-activist-after-order-by-swiss-authorities/
It is about mail they have different laws for vpn and i guess this confirms they are not owned by government or this would’ve been hush hush.
Sure, it what’s your threat model?
Even assuming a VPN is a government surveillance device …
- It protects me from surveillance by my ISP. This is the big one
- It protects me from other corporate and scammer surveillance
- It protects me from law enforcement abuse/overreach - however my data was obtained would not meet evidentiary standards
Look up parallel reconstruction
Besides that things can also simply be used to blackmail people - that can start very low level.
“Now Mr. Smith, you looked at gay porn on Saturday? Well, we don’t judge,but your wife sure would. Maybe you could tell us some gossip from Defence corp? Oh now that you did that - did you know that this is treason? We don’t judge, but a judge would. Maybe plant that device in your boss’s office?”
Besides that things can also simply be used to blackmail people - that can start very low level.
“Now Mr. Smith, you looked at gay porn on Saturday? Well, we don’t judge,but your wife sure would. Maybe you could tell us some gossip from Defence corp? Oh now that you did that - did you know that this is treason? We don’t judge, but a judge would. Maybe plant that device in your boss’s office?”
Besides that things can also simply be used to blackmail people - that can start very low level.
“Now Mr. Smith, you looked at gay porn on Saturday? Well, we don’t judge,but your wife sure would. Maybe you could tell us some gossip from Defence corp? Oh now that you did that - did you know that this is treason? We don’t judge, but a judge would. Maybe plant that device in your boss’s office?”
VPNs provides limited privacy and some security. For example, your traffic might be correlated to the traffic exiting at you VPN provider if enough netflow data is collected. Theoretically data from your ISP and your VPNs ISP would be enough. Today, countries and their agencies are probably collecting/trading enough netflow data for this purpose.
As a rule of thumb; since companies these days are very keen on getting in to the data trading market; you can safely assume that most of them has access, if it is legal.
For commercial offerings this is probably true for at least some of them, but creating your own VPN isn’t terribly difficult if you are serious about your privacy. I typically just use them when I travel to countries like China where I can’t get to a bunch of necessary services, so I don’t mind if they route my YouTube traffic through CIA headquarters, but if I was doing anything more than that I would just set up my own.
Part of the point of a VPN is there’s not a dedicated IP tied to you (or at least tying all of your activity together). That doesn’t provide any benefit besides a corporate/government firewall bypass unless a mass of people are using your server.
But then you don’t get the benefit of having increased privacy due to lots of people using the same IP.
Linka? Long shot, but message me if it’s you.
Which vpn have you found to work in china? Nord used to but doesn’t any more
I almost never trust any site that advertises any kind of VPN service (it’s always ranked by the best paying referrals) but this mirrors what I’ve seen in discussions.
From https://www.cloudwards.net/best-vpn-services-for-china/
Preferred VPN Choice: The general consensus among VPN users in China is that Astrill VPN is the most reliable option. However, it’s an incredibly expensive VPN, so it’s worth trying other cheaper options first. Surfshark is our top choice for best VPN for China as it has a solid reputation for working in the country while also offering affordable plans.
Alternative VPN Options: Other good options for China include CyberGhost, Proton VPN, Widscribe and Mullvad. NordVPN is also an option, but it’s not as reliable in China as the other six, so we only recommend it if you already have an account.
Censorship Evasion Strategy: Since VPNs are in a running battle with censorship, we recommend subscribing to multiple VPNs to ensure you have coverage at all times. No matter which VPNs you use, make sure you download them before going to China, as the download pages are often blocked.
Astrill is the only consistent one and I have to server hop at times.
No problem, just use a VPN to connect to it from another country! Wait…
Less and less vpn and vps companies provide services for mainland citizen. The main reason I heard of is when their server got blocked by the great firewall, those customers would immediately perform chargeback to get their money back even though it’s not the fault of the providers. You lose money on chargeback fees which means accepting mainland customers is very risky for them.
If that’s the case, that’s understandable. It’s always going to be a game of cat and mouse, so Id expect it’s quite an expensive market to break in to.
Could you use outline servers?
What homespun protocols you using from China? The regular ones like OpenVPN get blocked yeah.
There are a ton of obfuscating protocols that a VPN can run. obfs is one of the most popular. You can configure your VPN to appear as basically any traffic. HTTPS, DNS, QUIK.
I believe protonvpn is no log. I hope they make their servers ram only like mullvad eventually though, it would be a great improvement.
Is mullvad good? Are they no log?
Mullvad is the most private a VPN company can get. They literally accept cash by mail.
Mullvad is RAM only for a few months by now, no log since forever and regularly contributes to privacy related topics.
The thing is: you can’t trust a company when they say they are no log or RAM only. But you can trust what info you give them. Mullvad only has my IPs. No info about who I am otherwise. I send them 30€ twice a year and that’s it.
BUT: they don’t allow port forwarding anymore, if you need that, so they are not perfect.
Very. They’re probably the best out there. Fully anonymous payments, no log, ram disk servers, audited, I believe they’re open source. I think some downsides they have that I’ve heard is no port forwarding and they don’t have too many servers. However, they’re still very good nonetheless.
VPN companies actually use user created genuine traffic to hide bots and web crawlers and scrapers. That’s part of why their VPN’s are that cheap, they use your traffic to hide more expensive to buy bot traffic.