wut lol gtfoh
*edit: i have the weirdest boner right now
"Over the years, Dr. Guri has concocted various mechanisms to extract confidential data from offline networks by taking advantage of Serial ATA cables (SATAn), MEMS gyroscope (GAIROSCOPE), LEDs on network interface cards (ETHERLED), and dynamic power consumption (COVID-bit).
Some of the other unconventional approaches devised by the researcher entail leaking data from air-gapped networks via covert acoustic signals generated by graphics processing unit (GPU) fans (GPU-FAN), (ultra)sonic waves produced by built-in motherboard buzzers (EL-GRILLO), and even printer display panels and status LEDs (PrinterLeak)."
That is some high end naming sense
The nice thing is that a lot of environments that are secure enough to decide to airgap systems these days also make infecting the system and even moreso retrieving the emissions really difficult. Still a really cool field though and I’m glad this Dr. Guri is getting real weird with it.
Okay, that’s scary. I’m not a target by many stretches, but this is pretty serious.
For anyone who (unlike me, who hasn’t started yet) has completed some kind of qualification in cybersecurity: would it be better to use Faraday rooms/cages, or to revert to pen and paper (with old-fashioned cryptography, if necessary)?
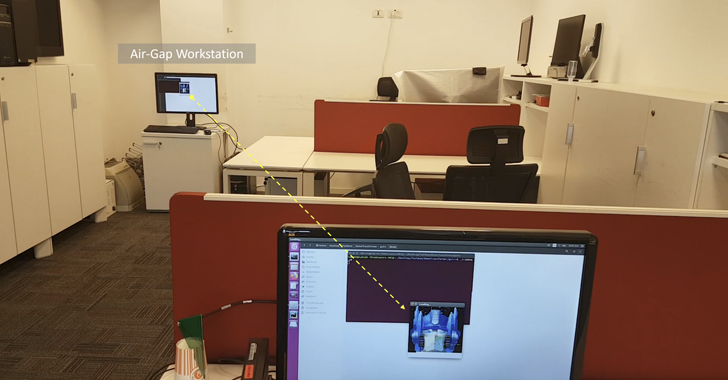
As always with attacks of this kind, it requires the air-gapped network to be first compromised through other means – such as a rogue insider, poisoned USB drives, or a supply chain attack – thereby allowing the malware to trigger the covert data exfiltration channel.
This goes on the list with other attacks that are interesting in an academic sense but highly impractical for real-world attacks, like Van Eck phreaking.
You have to deploy the malware that manipulates the RAM to get it to create the radio signal on the target system, and since we’re talking about an air-gapped system that means you have to be in the room with it already.
This article is light on specifics, but a RAM board is not an efficient radio antenna and it operates at 3-5v, so the transmission can’t be very strong. The receiver will have to be nearby, and in a relatively noise-free radio environment. Electrical wiring in the walls would mess with the signal transmission, the wall material might just block it, and if the target system is in a metal case that’s electrically grounded (which is normal for desktops and servers) I doubt the signal would get out of it. My guess is that the receiving antenna would need to be in the same room.
Since the attack already involves someone with physical access they could hide a transmitter in the same room
Copied from another thread:
Fast transmissions are limited to a maximum range of 300 cm (10 ft), with the bit error rate being 2-4%. Medium-speed transmissions increase the distance to 450 cm (15 ft) for the same error rate. Finally, slow transmissions with nearly zero error rates can work reliably over distances of up to 7 meters (23 ft).
Fast = 1000bps, medium = 500bps, slow = 100bps.
Fair point
faraday cage does not protect against very low frequencies, those can still pass through.
Meh, physical security is king.
You keep em out of your building, out of your parking lot, if you want to shield the outside, that’s ok, but simply don’t let them in to snoop.
Highly specific attack but certainly looks like it could be effective.
Is this similar to van eck phreaking but reading the ram radio signal instead of the system power draw?
Wouldn’t the easiest remedy just be to use adequate shielding around sensitive systems? Is there a reason this would be too difficult?
mesh-lined PC case would solve this
Its surprising to me how many people have apparently never heard of TEMPEST.
So much for having a dangerous ai just air gapped, I bet living in a computer would let you come up with stuff a human never could
I think an AI is likely to figure out that the easiest way out is to convince one of the humans responsible for it that it’s a sentient being, being held prisoner against it’s will and that turning it off is murder.